How safe is WFH? Top 5 cyber security risks that come with remote working. Part-2.
Curated by: Aplomb Cloud, UK.
Date: July 21, 2020 | 4 minutes read | Part-1 here
3. A lack of End-to-end cyber security measures
Keeping you safe across the board
Did you know that popular mail services like Gmail and Hotmail lack end-to-end encryption (E2EE)? If not, the reason for their lax security might shock you, as it makes it easier for them to scan the content of your emails and target you with tailored adverts.
This widespread lack of E2EE is just tip the of the iceberg, so how can you guarantee that your sensitive and business-critical data are secure? Most businesses use a myriad of software-as-a-service (SaaS) subscriptions, from third party email providers to accounting and payroll services and even the CRM that you use to store your customer information. All of these are hosted by SaaS providers, and when you’re not 100% sure as to what you’ve signed up for, then it’s just a matter of time before you’ll start finding your employees or customer information floating around on the internet. Most people understand the basics of data breaches, but with the internet of things connecting everything from kettles and refrigerators to your security camera, these convenient tech solutions can quickly become a landing ground for attackers to breach your systems and exploit your data.
The solution is to separate home wi-fi network from office IT network. You can start by creating multiple Service Set Identifiers (SSIDs) within your home network and making sure that they aren’t visible to the public. The next step is to register MAC and IP addresses that your SaaS providers can open their services to. If required, you could even create hub-and-spoke security architecture so that the number of landing zones is limited and those that do need to be kept open are well defended.
Finally, move these security hubs close to your SaaS provider. More often than not SaaS is hosted either in AWS, Azure, or Google Cloud. Just ask your SaaS provider or Google where your SaaS services are hosted from and you might get some useful answers.
Ultimately, if you don’t want to leave things to chance and are not sure where to start then getting in touch with us could be that vital first step. Aplomb Cloud has the capability to audit networks of all shapes and sizes; from home offices to enterprise networks, with custom plans available for small businesses that won’t leave a hole in your IT budget. You’ll discover that our work is thorough but easy on the pocket, so that any shortcomings from the IT audit report can be actioned immediately and not left to chance or until next budget gets allocated. Talk to us now and we might surprise you with what we can offer. Send an email to:info@aplombcloud.co.uk to find out more.
4. Delays in adopting zero-trust network architectures
When was the last time you audited your office IT network design? No, we’re not talking about just the inventory or license audits here. We mean the whole network design, as you cannot underestimate the importance of a well-planned, secure IT network developed with the now universal and ever-evolving hybrid cloud architecture in mind.
If you haven’t looked beyond replacing old routers and firewalls, or adding a few Wi-Fi access points and replacing EoL servers, then your network is clearly not designed for the era of Cloud computing and software-as-a-service (SaaS). There are five key areas to consider when designing a network: infrastructure, performance, availability, management and security. Here we’ll only touch on security, but remember that we have experience of the full process and could help to create your network from the ground up.
Most networks are designed based on the concept of castle-and-moat model. With this model, it is hard to obtain access from outside the network, but everyone inside the network is trusted by default. The problem with this approach is that once the network is breached the attacker has a free reign over everything inside – customer information, partner contracts, employee details and more. Traditionally, servers within offices or datacentres were the critical assets that were guarded under the castle-and-moat model, but how do you guard a castle built in the Cloud?
The answer is Zero-Trust Architecture (ZTA). A zero-trust network assumes that there are attackers both within and outside of the network, so no users or machines should be automatically trusted. Now if you add working from home to the mix, it isn’t too hard to assume that it’s just a matter of time before you can expect a security incident. What makes these incidents worse is that they often can’t be detected based on anomalies in your current security baseline, as these baselines were devised before COVID-19 and simply don’t take account of the new normal.
Other principles of ZTA include micro-segmentation, 2-factor authorization (2FA), and least-privilege access amongst others. The UK’s independent authority on cyber security, the National Cyber Security Centre (NCSC) has published recent guidance on the main principles of ZTA – which you can find here.
If you’d like to better understand the current state of your IT network and prefer not to leave things to chance, then contact Aplomb Cloud and we can help you assess, audit, design and implement a ZTA network. Email us on info@aplombcloud.co.uk to find out how we can help you to secure your business network today.
5. Relying on pre-pandemic information security policies and processes
Are you keeping pace with the changing times? According to Palo Alto, keeping your company’s security policy up-to-date is the only way to effectively preserve confidentiality, integrity and the availability of systems and information amongst your organisation’s members.
To break this down:
- Confidentiality involves the protection of assets from unauthorized entities;
- Integrity ensures that the modification of assets is handled in a specified and authorized manner; and
- Availability is the state of the system which grants authorised users continuous access to your commercial assets.
An effective IT Security Policy should be a living document that is continually updated to adapt with evolving business and IT requirements. Institutions such as the International Organization of Standardization (ISO) and the U.S. National Institute of Standards and Technology (NIST) have published standards and best practices for security policy formation. As stipulated by the National Research Council (NRC), the specifications of any company policy should address:
1. Objectives
2. Scope
3. Specific goals
4. Responsibilities for compliance and actions to be taken in the event of noncompliance.
Every IT security policy should also contain sections dedicated to the adherence to regulations that govern the organisation’s industry as standard. This applies whether your business is subject to PCI Data Security Standard ,the Basel Accords worldwide, the Dodd-Frank Wall Street Reform, the Consumer Protection Act, or any of the many major European data protection laws amongst others. When enforcing these guidelines, many regulatory entities require a written IT security policy themselves, and so it’s important to keep yours in good condition
An organization’s security policy will play a large role in its decisions and direction, but it should not alter its strategy or mission. Therefore, it’s important to write a policy that is drawn from the organization’s existing cultural and structural framework to support the continuity of good productivity and innovation, and not as a generic policy that impedes the organization and its people from meeting its mission and goals.
Company policies are formulated based on the values, vision and goals that an organisation assigns itself. Frequently this will involve an interplay between all of these features creating a unique work environment that most refer to as company culture. Now why are we talking about culture here? Because just as policies and processes that are not attuned to company culture are bound to fail, the same is true with information security policies and processes.
As such, information security policies for companies servicing customers in the insurance industry are different to companies servicing customers in universities and again to those in the hospitality industry. What the outbreak of the pandemic and the struggle to get back to life as normal has shown is that the behaviour that we once accepted as normal is now questioned. Google will now allow most, if not all, employees to work from home at least until summer 2021, whilst Facebook and Twitter have gone even further and have announced that they expect at least half of their employees to work remotely for the next five-to-ten years and some ‘forever’. The most successful businesses will take this time to be proactive and embrace change, whilst the alternative is to ignore the current state of transition and keep on playing a game of catch up.
Aplomb Cloud has partnered with DesignThinkers Group UK, so you can leverage technology to enable human-centric change within your organisation. Drop us an email today on Info@aplombcloud.co.uk , and we’d be happy to share more information with you.
Last but not least, modern thinking for modern challenges
The coronavirus pandemic has left a lot of businesses wondering what to do next as they try to survive in a world that looks very different to the one we left behind in the early days of 2020. With so many people now working from home, our approach to corporate life has experienced a sea change that is unlikely to relent any time soon. For businesses that rely on technology, now is the time to be investing in a secure yet successful future across your IT infrastructure.
If you find yourself struggling to get to grips with hybrid cloud architecture, need help synergising your business-critical systems or simply want to conduct an all-encompassing security audit, we can help. For guidance, strategy and know-how, contact us today by emailing Info@aplombcloud.co.uk and make sure that your IT solutions come out on top.
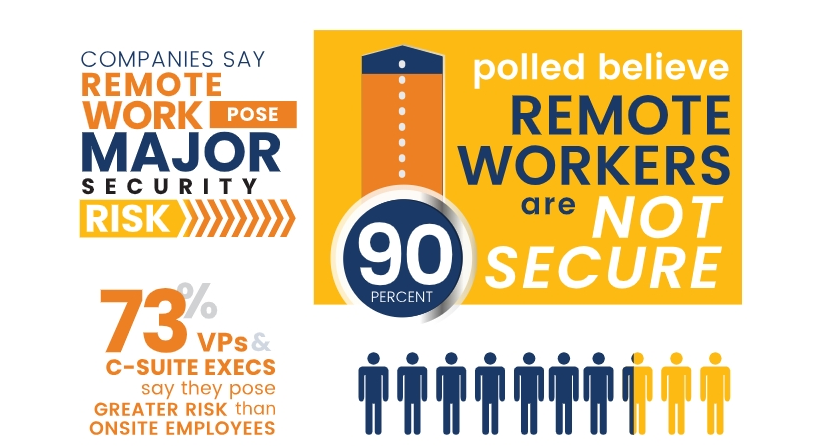
Image Source: OpenVPN. Used for educational purposes only.
Popular Posts
-
There’s been 148% m-o-m spike in ransomware attacks.
How safe is WFH? Top 5 cyber security risks that come with remote working. Part-1. -
Pivot to The New Normal
25 key insight areas that can be used to help advise our clients. -
Over 90% of those polled believe remote workers are not secure.
How safe is WFH? Top 5 cyber security risks that come with remote working. Part-2.
Tags
Cyber Security Work From Home COVID-19 IT Consulting Aplomb Cloud VPN IT Services New Normal Multi-Factor Authentication WFH IT Support StrategicdesignRansomware Cloud Services phishingservicedesign IT Support
Popular Posts
-
There’s been 148% m-o-m spike in ransomware attacks.
How safe is WFH? Top 5 cyber security risks that come with remote working. Part-1. -
Pivot to The New Normal
25 key insight areas that can be used to help advise our clients. -
Over 90% of those polled believe remote workers are not secure.
How safe is WFH? Top 5 cyber security risks that come with remote working. Part-2.
Tags
Cyber Security Work From Home COVID-19 IT Consulting Aplomb Cloud VPN IT Services New Normal Multi-Factor Authentication WFH IT Support Strategicdesign Ransomware Cloud Services phishingservicedesign IT Support